A lot of people that hear about VPN’s but don’t really know why they would need to use one in the first place but there are so many dangers on the internet these days that it is really becoming a necessity these days.
A VPN (Virtual Private Network) or simply a virtual network, is a special type of secured network. These networks allow individuals and companies to share and access information from any computer anywhere. The networks are private because access to them is restricted to certain users. They are considered virtual networks because they use internet to connect users, rather than a direct connection so it is just like having two computers next to each other connected via a network cable but instead it is via a VPN . Over the past few years, VPN is becoming increasingly popular as it has proven to be very secure and cost effective.
Dangers When Not Using A VPN:
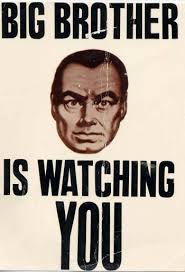
- Government agencies spying on your online activities.
- Your ISP (Internet Service Provider) monitoring your online activities such as sites you visit and what you download.
- The Network Administrator at your school, work, or any where you access WiFi monitoring your online activities.
- Hackers trying to steal your information.
- Identity Theft.
- Bank accounts emptied.
- Personal things like your photos stolen.
- Email accounts hacked.
- Social Media Accounts hacked.
- Industrial Espionage, (a work competitor trying to steal your trade secrets).
- Online marketing companies gathering all of your personal information and doing whatever they like with it so you get bombarded with marketing products. (Like whemn you look at a product once and then you are followed around the internet with those ads).
On top of all of this do you know that while you are using WiFi ANYWHERE (including your home if there is not a VERY secure password) that you just have all of your personal info out in the open for anyone to take? There are simple free programs available on the internet that can intercept your details while on WiFi so a predator can gain access to your computer and accounts to steal your files, photos, other personal info, username and passwords so they can gain access to all of your online accounts and do whatever they like with them.
It is happening more and more these days where groups of criminals target people online and steal their identities so they can then open up credit card accounts in their name and then put them into massive debt that is more often than not is extremely hard to disprove it was actually you. So many people have been ruined by this lately.
Even now Comcast, one of the USA’s biggest ISP’s, are monitoring its customers and warning them to stop using Tor browser if they are otherwise they will be kicked off! There reasoning is that they think that if you are using Tor browser then you must be doing something illegal. There has never been such an invasion of your online and offline activities as there is now and it is getting worse.
Benefits of a VPN
The level of protection you get from using a VPN today is so good that even your ISP (Internet Service Provider) will not even know what you are doing. You can even use the VPN in some circumstances to speed up your internet speed as they all they see is encrypted data and that is all. This also means that any one trying to see what you are doing online such as the government, hackers, network administrators at your work or school or parents, anyone that wants your private information can not see a thing you are doing online.
Some benefits include:
- VPN is extremely secure.
- VPN is extremely anonymous if from the right provider.
- You can access blocked content on the internet.
- You can access blocked sites while overseas (eg Facebook, Twitter, YouTube is blocked in certain countries).
- You can access blocked streaming services from overseas like HULU, NETFLIX, Spotify, Pandora, BBC, iPlayer, Skype etc.
- You can access P2P file sharing hidden.
- VPN allows users/employees to access information from remote locations, making collaboration easy when users are scattered around the globe.
- The ability to access information remotely permits users to telecommute, which saves money and time used in transport.
- Because VPN uses internet rather than leased wide area network line, the cost of linking computers with a VPN is much lower compared to other methods.
VPN Technology
VPN works by creating a tunnel that connects the two end points. All information is securely transferred through these tunnels. The tunnels are virtual connections which have replaced older physical systems such as dedicated leased lines that organizations used to connect their local networks together.
There are different types of protocols used and also different levels of encryptions that serve different purposes. If you are after maximum security and anonymity then you would want to use the OpenVPN protocol which provides an excellent level of both.
Virtual tunnels involve sending and receiving packets of encrypted information which is encapsulated within outer packets. The outer packets are also encrypted and pre-programmed with their source and destination; only the destination points are configured to decrypt them.

Packets are used in conjunction with authentication measures at each end to ensure the correct user and device is accessing the connection. If a person attempts to intercept the packets as they take their journey across the public networks, they will only be able to determine the gateway/firewall server that they are heading towards, but none of the data contained within them or even their final destination on the local network.
So the sooner you come to terms that the internet is not longer open, free and anonymous the sooner you will come to realize that using a VPN is the smart thing to do if you value your privacy and freedoms that you think you currently have .

The level of protection you get from using a VPN today is so good that even your ISP (Internet Service Provider) will not even know what you are doing. You can even use the VPN in some circumstances to speed up your internet speed as they all they see is encrypted data and that is all. This also means that any one trying to see what you are doing online such as the government, hackers, network administrators at your work or school or parents, anyone that wants your private information can not see a thing you are doing online.
What people don’t know when they look at and receive this site/program, is you can create your own VPN for free. You don’t have to pay to get a VPN. There are many ways to do this. Mainly just type in create a free VPN for my device.
Why isn’t there an option for the Untied States of America when asked for your country of origin??
Is it because AmeriCO’s has become the world’s largest terrorist evil Empire on Earth??
Thanks for the comment Randy.
That is because most people living in America have access to everything already.
So we have catered to people from other parts of the world.
Though people living America can use VPN services as well.
Very interesting. I will take heed.
Its very very nice
Hi Lexcorps.
Indeed it is.
Very interesting information and well explained I’m using OpenVPN and it’s a very useful application.
Cheers.
Hi Noa.
Glad you are finding OpenVPN as a secure VPN protocol.